Aljosha Judmayer successfully defended his PhD thesis
We congratulate Aljosha Judmayer to successfully defending his PhD thesis “Pay to Win – Algorithmic Incentive Manipulation Attacks on Permissionless Cryptocurrencies” and thank Rainer Böhme and Bryan Ford for their service as examiners.
The digital exchange of units of financial value, commonly referred to as money, is a fundamental aspect of our technology-driven society. The rise of cryptocurrencies, as well as their downsides, has sparked a development in digital financial technologies of different forms. This also lead to initiatives on international level (keyword: Digital Euro). The long-term effects of all these developments in the area of digital financial technologies as well as their consequences are still unclear.
Understanding the interplay between various technologies and the relationship between technology and society is crucial for assessing both the risks and opportunities presented by interconnected cryptographic financial systems. This work contributes to this understanding by examining the potential for technology-facilitated bribery designed to alter the motivations of both system operators and users, thereby enhancing our grasp of its implications.
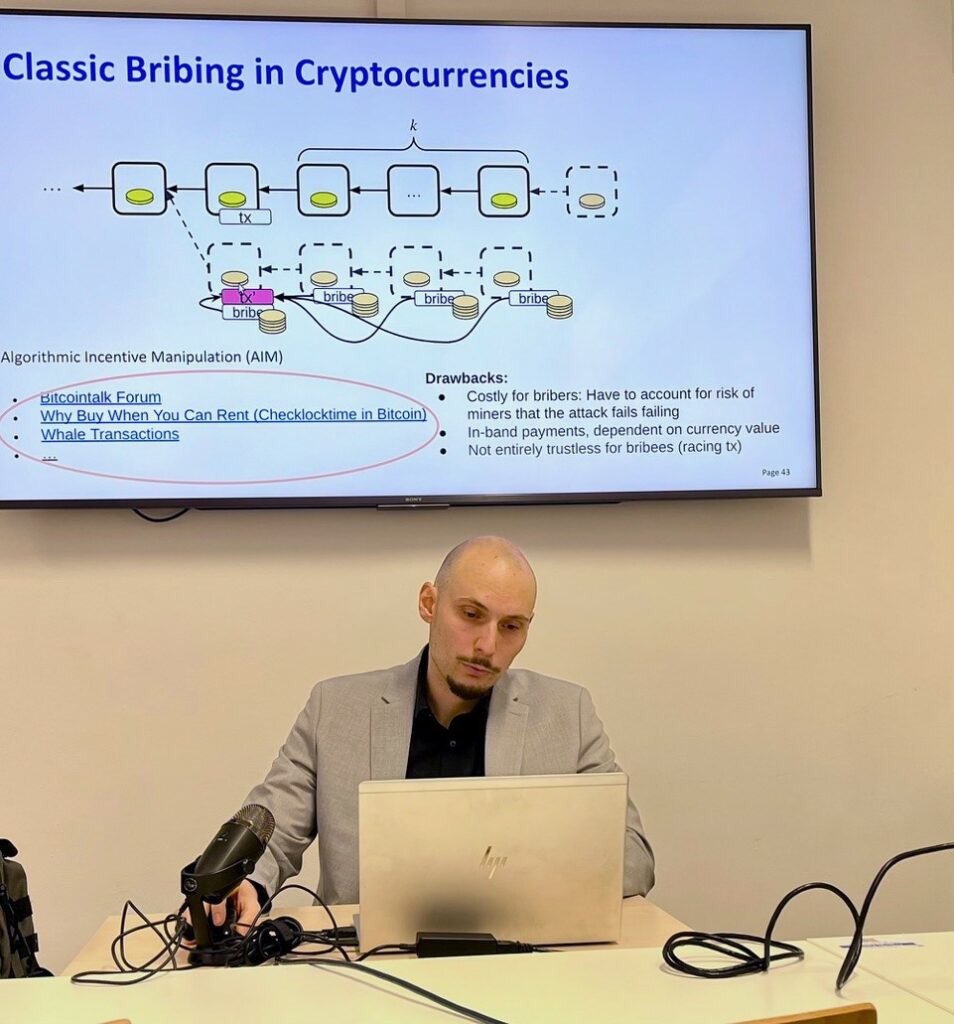
In this thesis a new category of attacks called algorithmic incentive manipulation (AIM) is presented, which also summarizes related attacks targeting the incentives of participants under this new category. Although, the focus of the thesis is on public permissionless Cryptocurrencies, AIM theoretically affects any centralized or decentralized digital financial systems in which cryptographic proofs over the state of the system could be produced.
AIM attacks programmatically offer rewards, or issue threats, which change the incentives of economically rational players. Thereby, an attacker can increase the chance that the targeted system reaches a favored state. Depending on the motives, this state must not necessarily be profitable for the attacker. However, if the desired state leads to profits for the attacker, shares of this profit can be used in algorithmically enforceable side payments for the colluding players of the attack. In other words, the attacker pays to win.
It is well known in game theory that collusion and side payments pose severe challenges to mechanism design. However, the extent of the problem with regard to permissionless cryptocurrencies or digital financial systems exposing cryptographic proofs is not conclusively understood yet. This thesis lays the necessary ground-work for a better understanding: It describes the problem, systematizes related attacks, provides new attacks (including a proof-of-concept), evaluates the success probability and profitability, and proves that it is not possible for permissionless cryptocurrencies based on Nakamoto Consensus to prevent AIM by technical means alone.
In a world where multiple cryptocurrencies co-exist and can be cryptographically interlinked, the availability of other (external) cryptocurrency resources participants care about is a plausible assumption. This not only requires us to reconsider the achievable economic security guarantees of permissionless cryptocurrencies and certain design decisions which amplify the problem, but also carefully consider the design of any public cryptographically backed digital financial system.
Aljosha and our distributed systems group have had some excellent publications in the last years:
Opportunistic Algorithmic Double-Spending: How I learned to stop worrying and love the Fork (2022)
Stifter, N., Judmayer, A., Schindler, P., Weippl, E. (2022). Opportunistic Algorithmic Double-Spending:. In: Atluri, V., Di Pietro, R., Jensen, C.D., Meng, W. (eds) Computer Security – ESORICS 2022. ESORICS 2022. Lecture Notes in Computer Science, vol 13554. Springer, Cham. https://doi.org/10.1007/978-3-031-17140-6_3
RandRunner: Distributed Randomness from Trapdoor VDFs with Strong Uniqueness (2021)
Network and Distributed Systems Security (NDSS) Symposium 2021 in cooperation with USENIX 21-25 February 2021, Virtual. ISBN 1-891562-66-5. https://dx.doi.org/10.14722/ndss.2021.2311
HydRand: Practical Continuous Distributed Randomness (2020)
P. Schindler, A. Judmayer, N. Stifter and E. Weippl, “HydRand: Efficient Continuous Distributed Randomness,” 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 2020, pp. 73-89, doi: 10.1109/SP40000.2020.00003
Proof-of-Blackouts? How Proof-of-Work Cryptocurrencies Could Affect Power Grids (2018)
Ullrich, J., Stifter, N., Judmayer, A., Dabrowski, A., Weippl, E. (2018). Proof-of-Blackouts? How Proof-of-Work Cryptocurrencies Could Affect Power Grids. In: Bailey, M., Holz, T., Stamatogiannakis, M., Ioannidis, S. (eds) Research in Attacks, Intrusions, and Defenses. RAID 2018. Lecture Notes in Computer Science(), vol 11050. Springer, Cham. https://doi.org/10.1007/978-3-030-00470-5_9
Condensed Cryptographic Currencies Crash Course (C5) (2016)
CCS ’16: Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security October 2016. Pages 1857–1858. https://doi.org/10.1145/2976749.2976754
The Other Side of the Coin: User Experiences with Bitcoin Security and Privacy (2016)
Krombholz, K., Judmayer, A., Gusenbauer, M., Weippl, E. (2017). The Other Side of the Coin: User Experiences with Bitcoin Security and Privacy. In: Grossklags, J., Preneel, B. (eds) Financial Cryptography and Data Security. FC 2016. Lecture Notes in Computer Science(), vol 9603. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-662-54970-4_33