SBA @ Security Forum Hagenberg
Our colleague Reinhard Kugler gave a talk titled Resistence is futile! How a Linux system is assimilated using eBPF rootkits on May 5, 2026.
© Sebastian Schrittwieser
Abstract
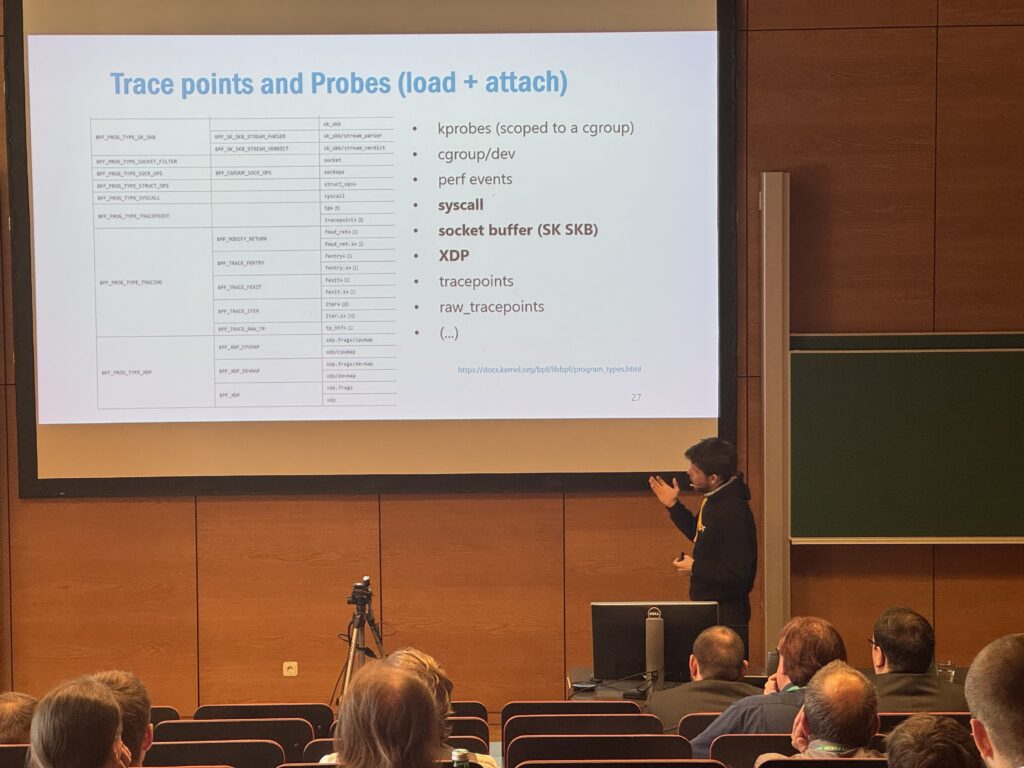
A new trend arises: abusing the Kernel to backdoor and assimilate Linux systems using the eBPF. The integration of the eBPF technology in the Kernel allows attackers to change the behavior of the live system.
Aside from defensive means, the question remains: how can it be exploited and what can an attacker do with those capabilities? From an attacker’s view, the eBPF technology offers several ways to abuse the operating system. This is not limited to system calls, but expands on the network, the file system, containers and much more. In a context of a Security Operations Center (SOC) this poses a significant threat, that could blindside the secure operation of an infrastructure.
In talk we focus on post-exploitation techniques from a privileged attacker’s perspective. Since an attack never stops after a successful privilege escalation, we approach the areas of assimilation of a Linux system. This compromised use system hides files, blocks network and file operations and manipulates access.
A decade of enumeration attacks in WhatsApp and other recurring vulnerability patterns in mobile apps was the title of a talk by our key researcher Sebastian Schrittwieser and David Schmidt, PhD student working in the CD Laboratory AsTra at the University of Vienna.
© David Schmidt & Sebastian Schrittwieser
Abstract
Over the past 15 years, we have repeatedly analyzed popular mobile messengers and widely deployed mobile applications. Despite changes in platforms, development frameworks, and threat models, a striking pattern persists: the same classes of security vulnerabilities continue to reappear. While implementations evolve, the underlying attack principles remain largely unchanged. This talk presents a longitudinal view on mobile app security, with a particular focus on enumeration attacks in mobile messengers. We first analyzed such attacks in 2011 and revisited them again in 2025. Our recent analysis shows that the same fundamental attacks are still feasible today. In fact, the situation has worsened. Modern platforms expose a much larger attack surface due to richer APIs, a much larger user base, and complex backend ecosystems that have grown substantially over time.
Speaker
Sebastian Schrittwieser is key researcher at SBA Research and a senior scientist in the security and privacy research group at the University of Vienna. Since 2024, he heads the Christian Doppler Laboratory for Assurance and Transparency in Software Protection. His research focuses on software protection, the security of large language models, and psychological aspects of information security. He has published in leading venues including ACM CCS, ACM KDD, NDSS, USENIX Security, ACSAC, and ACM Computing Surveys, and has served as program chair for several conferences and workshops, including ARES 2018 and ARES 2025.
David Schmidt is a PhD student working in the CD Laboratory AsTra at the University of Vienna. His work focuses on large-scale analysis of the mobile app ecosystem, developing automated techniques to uncover security and privacy vulnerabilities. By accelerating the detection of security issues, his research aims to strengthen the overall security of mobile apps.
About the forum
The Security Forum is the annual ICT security conference of the Hagenberger Kreis and traditionally takes place on two days in spring. Visitors are offered technical as well as management-oriented presentations on both days. For nearly 20 years now the event organized by the FH Oberösterreich is a guarantee for high quality talks and a professional atmosphere. The participants come from